The Signicat Blog
-
Blog
What brown M&Ms can teach you about contracts
-
Blog
Kubernetes: Your Sidecar configurations are drifting
-
Blog
The onboarding advantage: how operational efficiency boosts conversion
-
Blog
Empowering Women in Tech: Signicat's Commitment to Equality and Diversity
-
Blog
Building trust into every signature
-
Blog
Stand up to the scamdemic: how Signicat helped reduce fraud costs and fraud rate by 75%
-
Blog
Test, buy and deploy digital identity solutions in days, not weeks (with no meetings)
-
Blog
From Vision Towards Reality: The Journey of Establishing a European Digital Identity
-
Report
New European Identity - eIDAS 2.0
-
Blog
First 5 experiences on the journey to build a data-driven company
-
Blog
Planned Difference: Consciously diverging from standards
-
Blog
Signicat now offers Local IdP in addition to MitID Business as a login and signing option
-
Blog
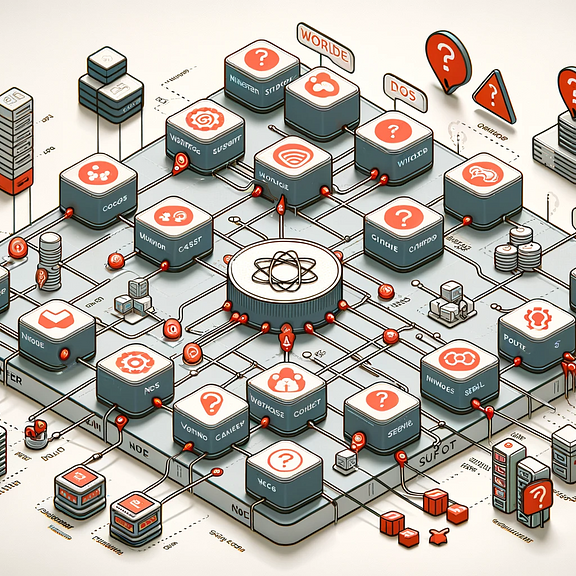
Kubernetes: Don't use NodeLocal DNSCache on GKE (without Cloud DNS)
-
Blog
Forrester Total Economic Impact™: Discover the ROI of Signicat
-
Blog
Digital identity wallets: exploring benefits and luxury traps
-
Blog
Signed, sealed..but maybe not compliant?